This post will cover the claim that for 1Password you key and master password are not sent outside of your client.
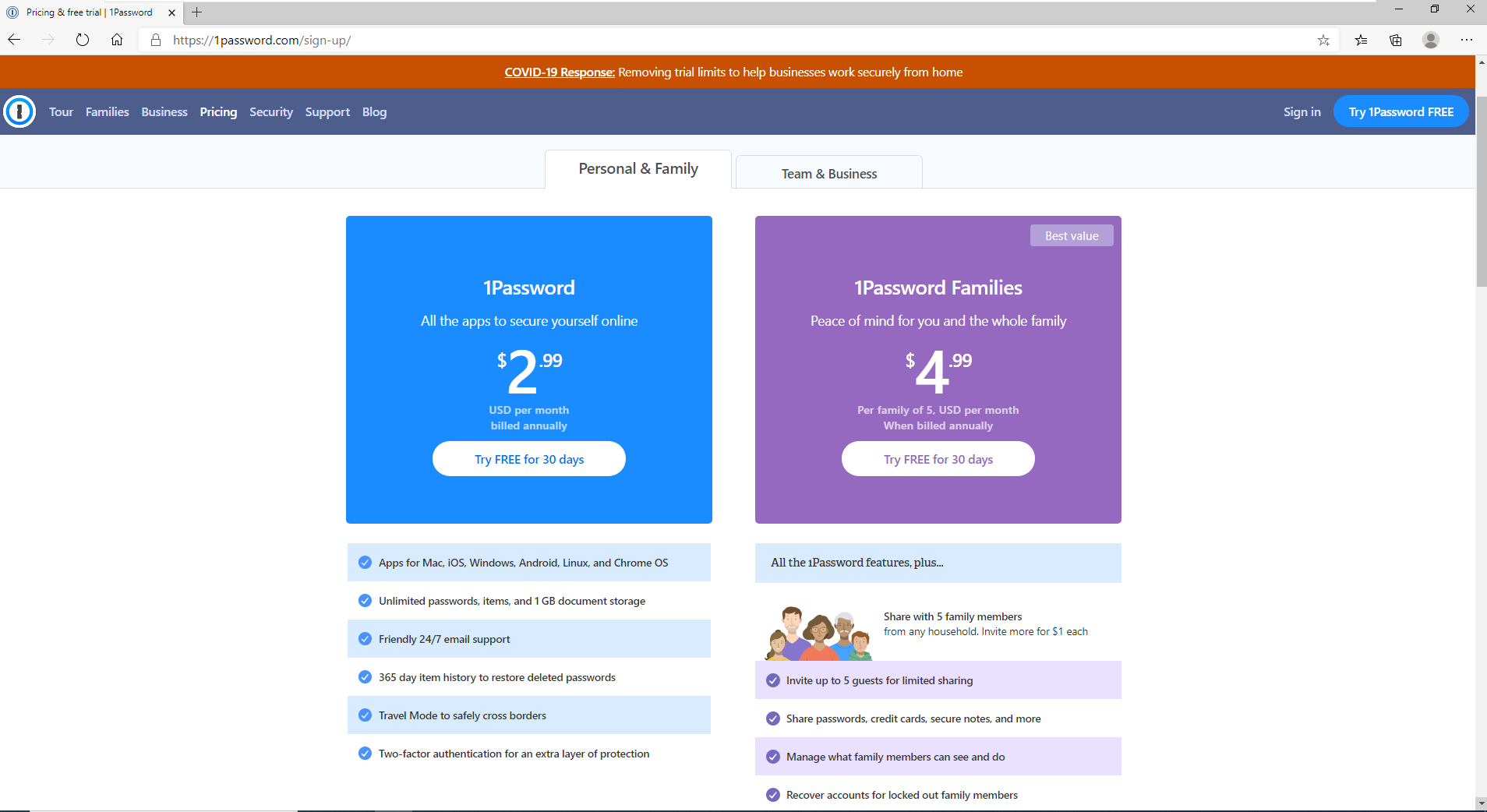
Signing Up
The very first step involves setting up a 1Password account. For this I simply created a temporary test account:
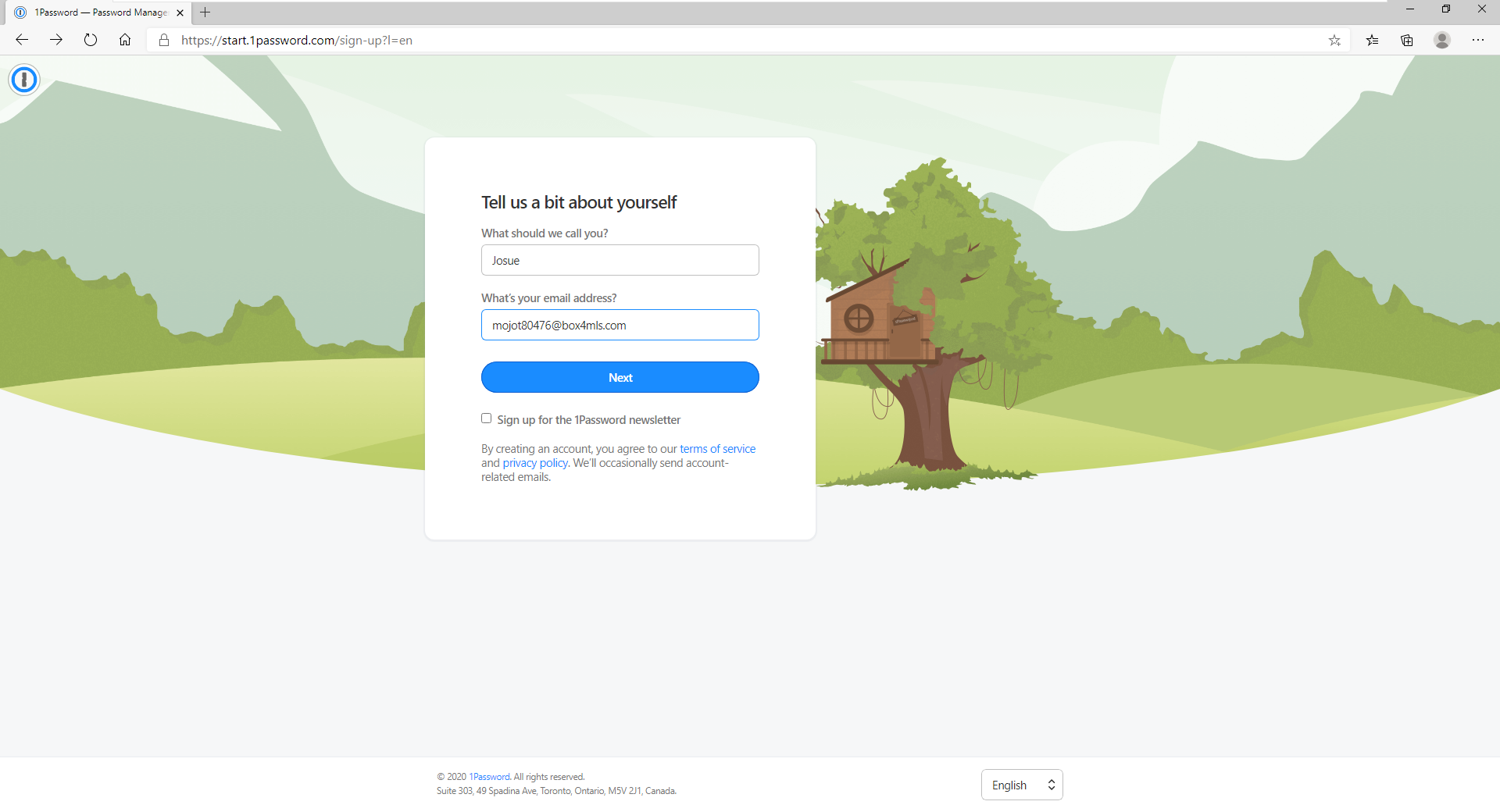
After following the several screens to setup things such as payment information you are then prompted to set the password on your account:
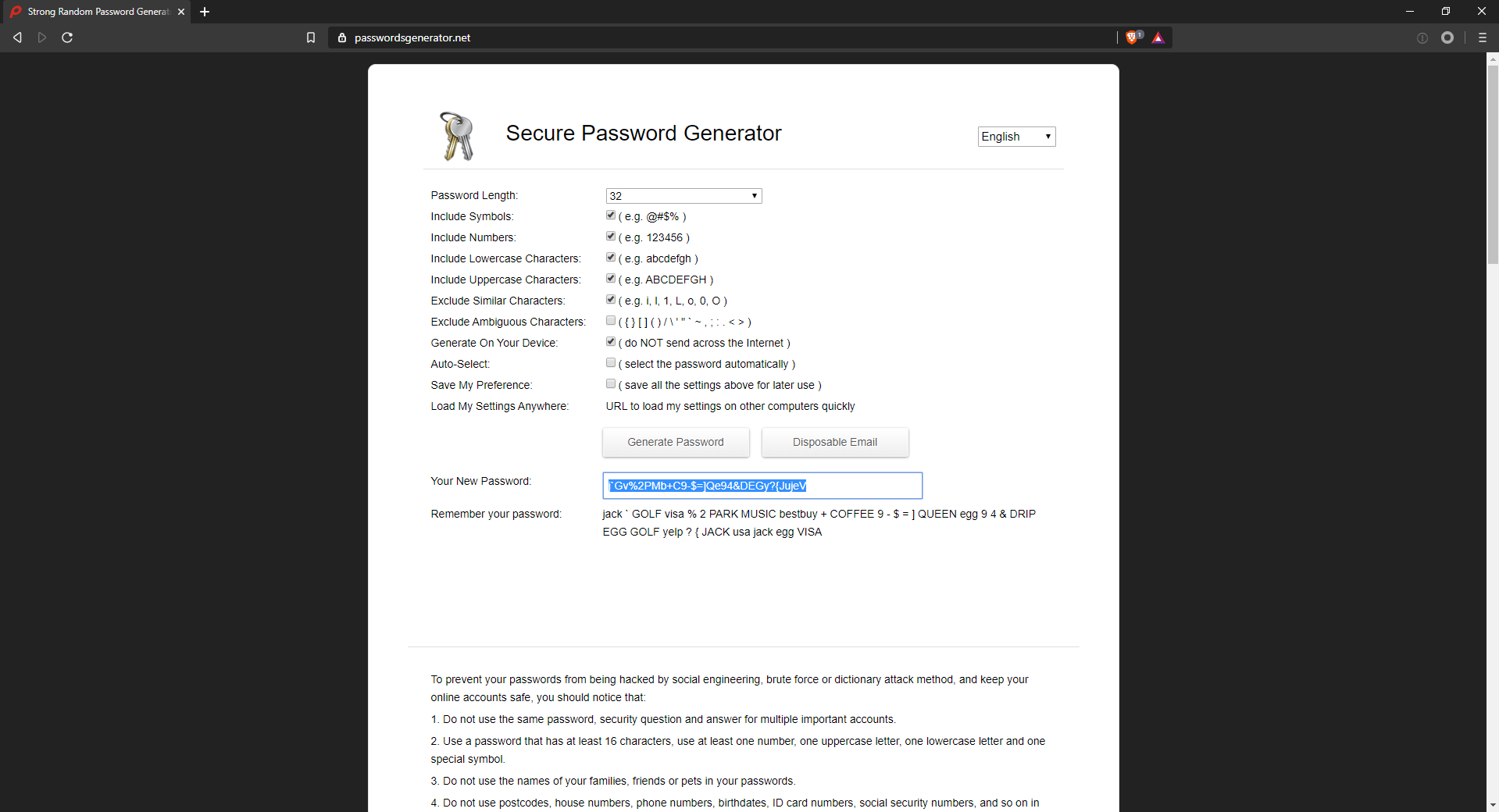
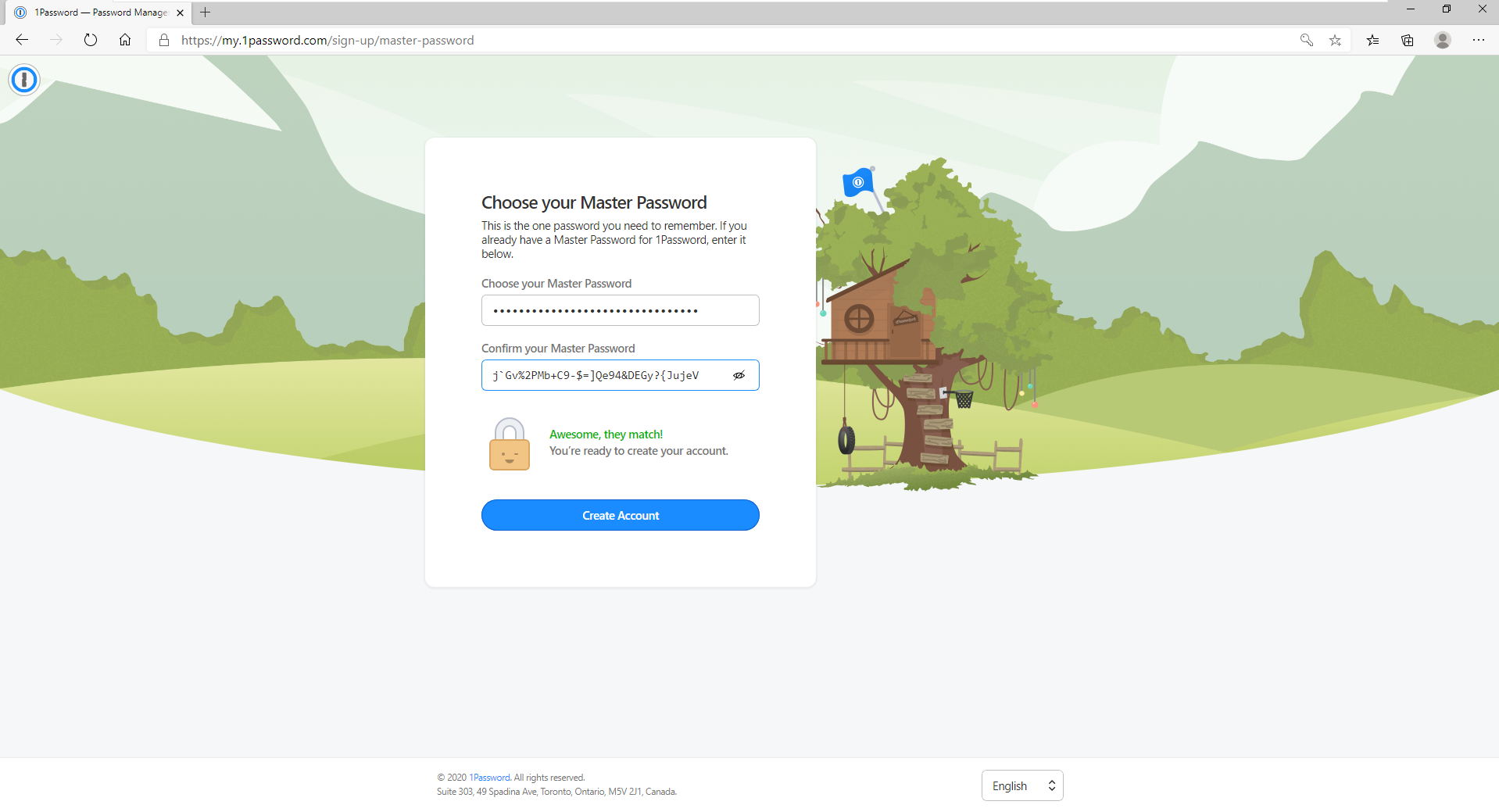
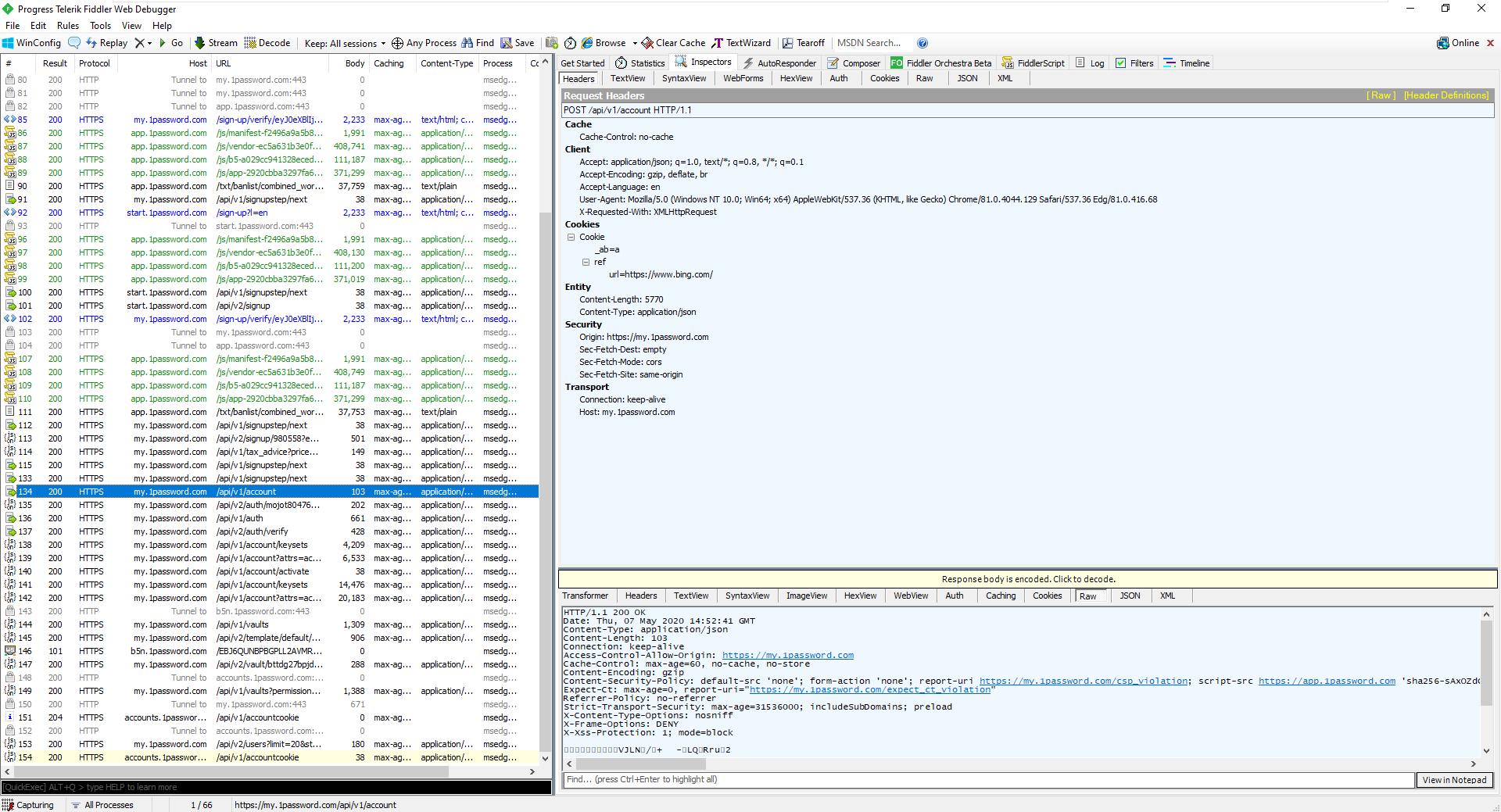
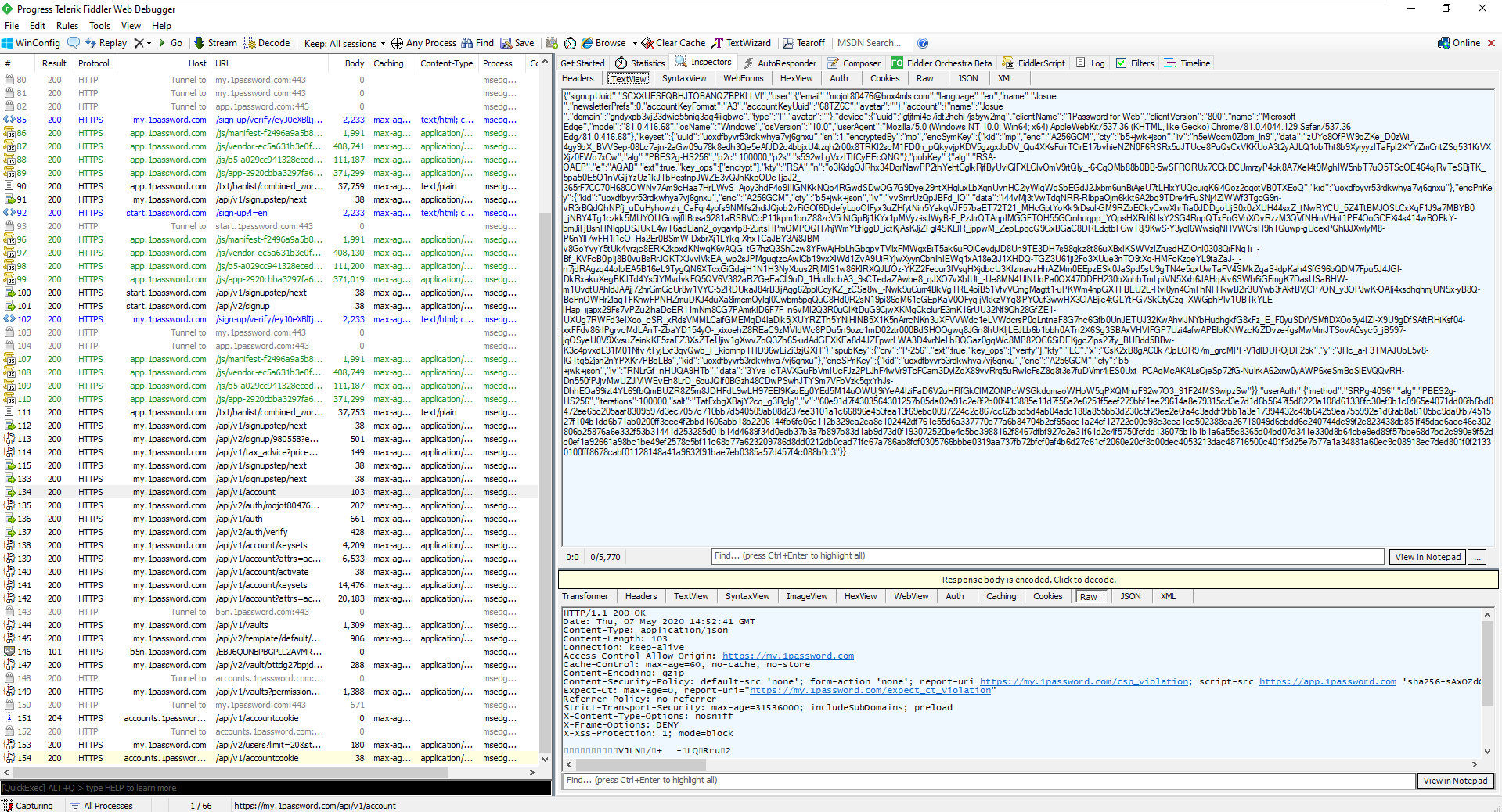
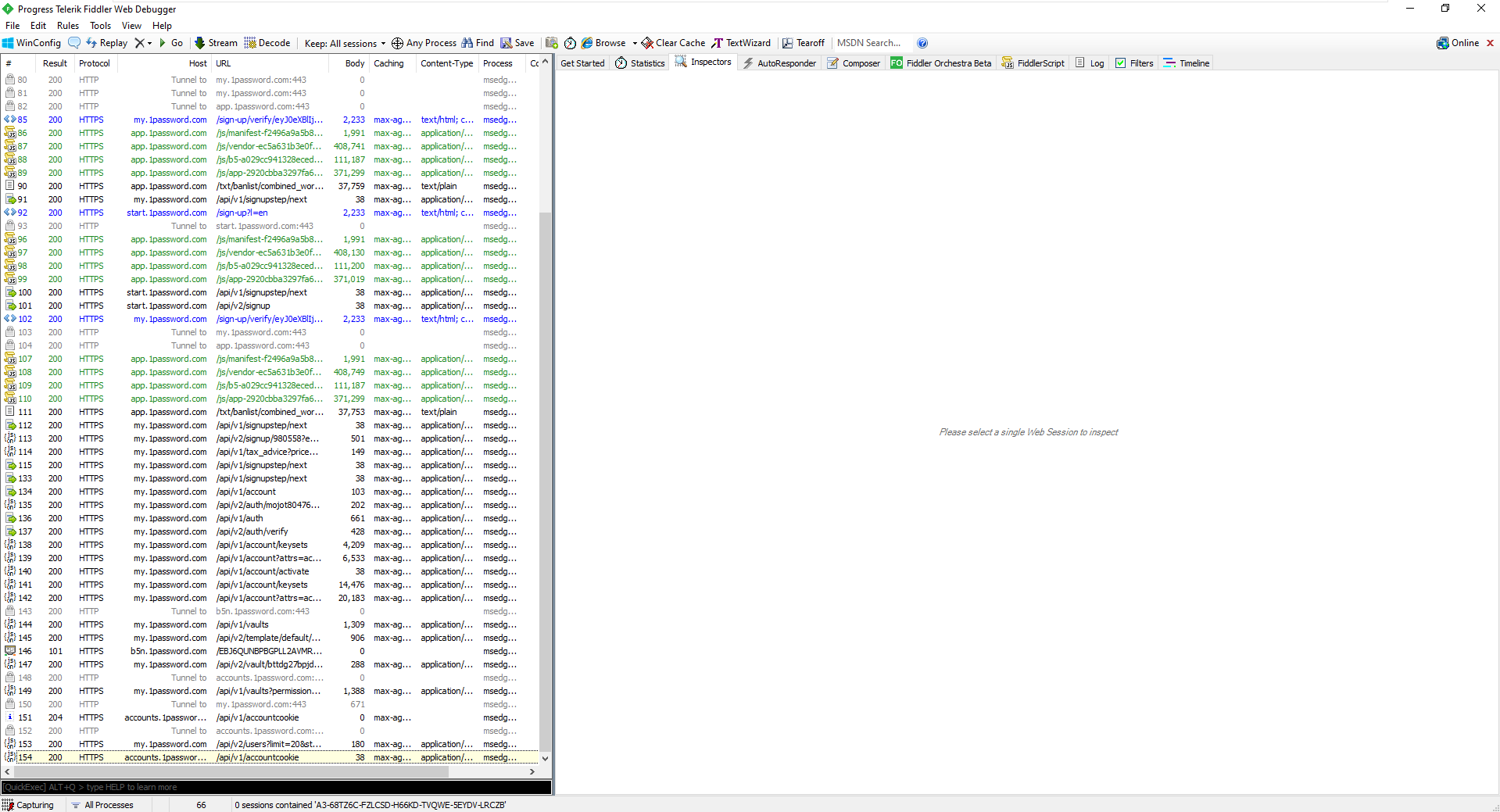
The interesting thing to note is that the password itself is not sent onto 1Password:
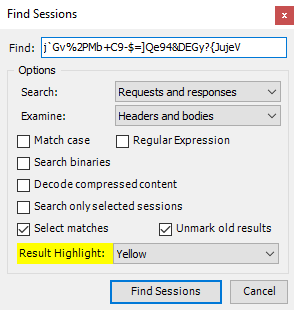
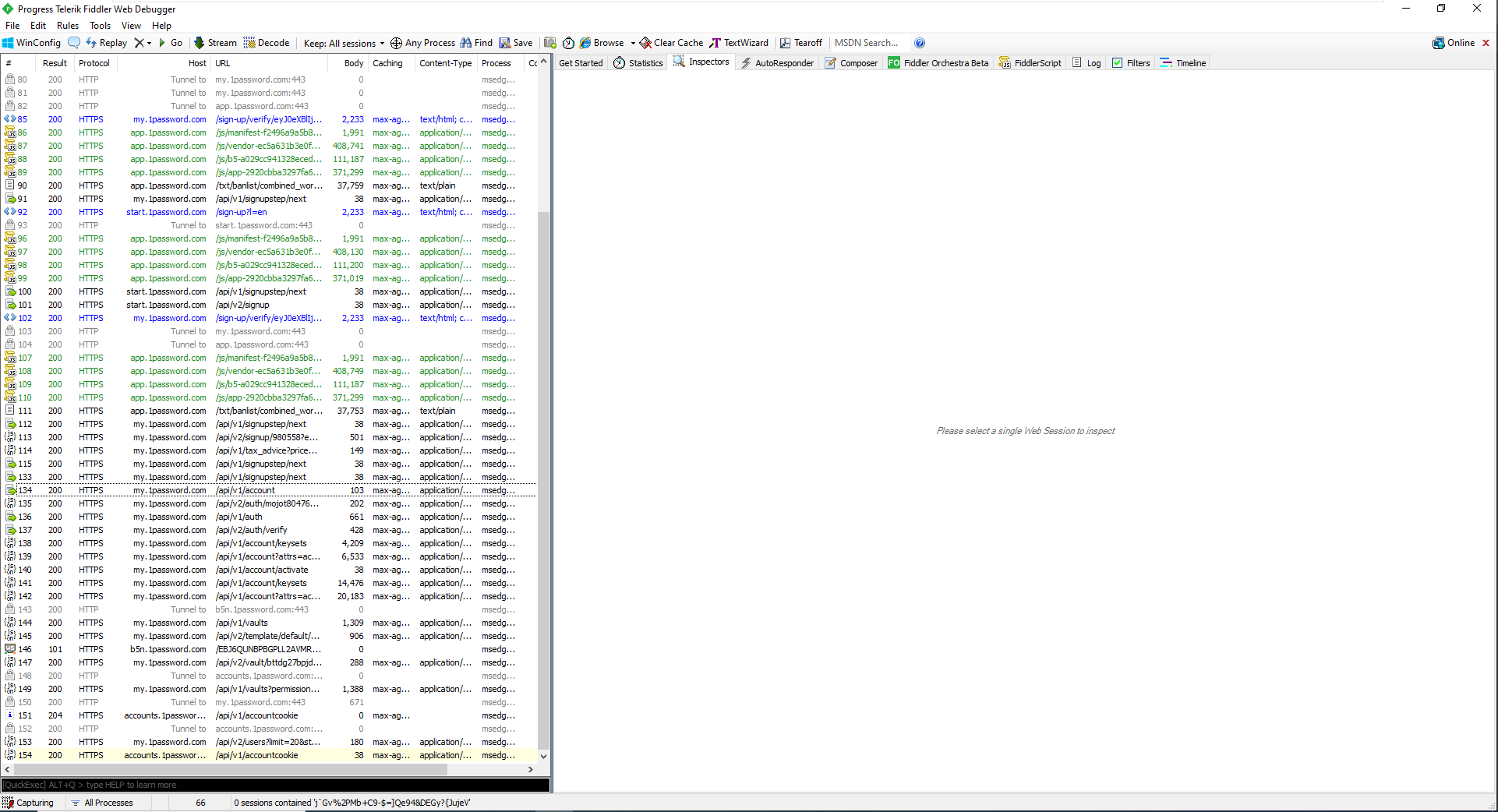
And to illustrate this I used Fiddler's find feature which return zero hits:
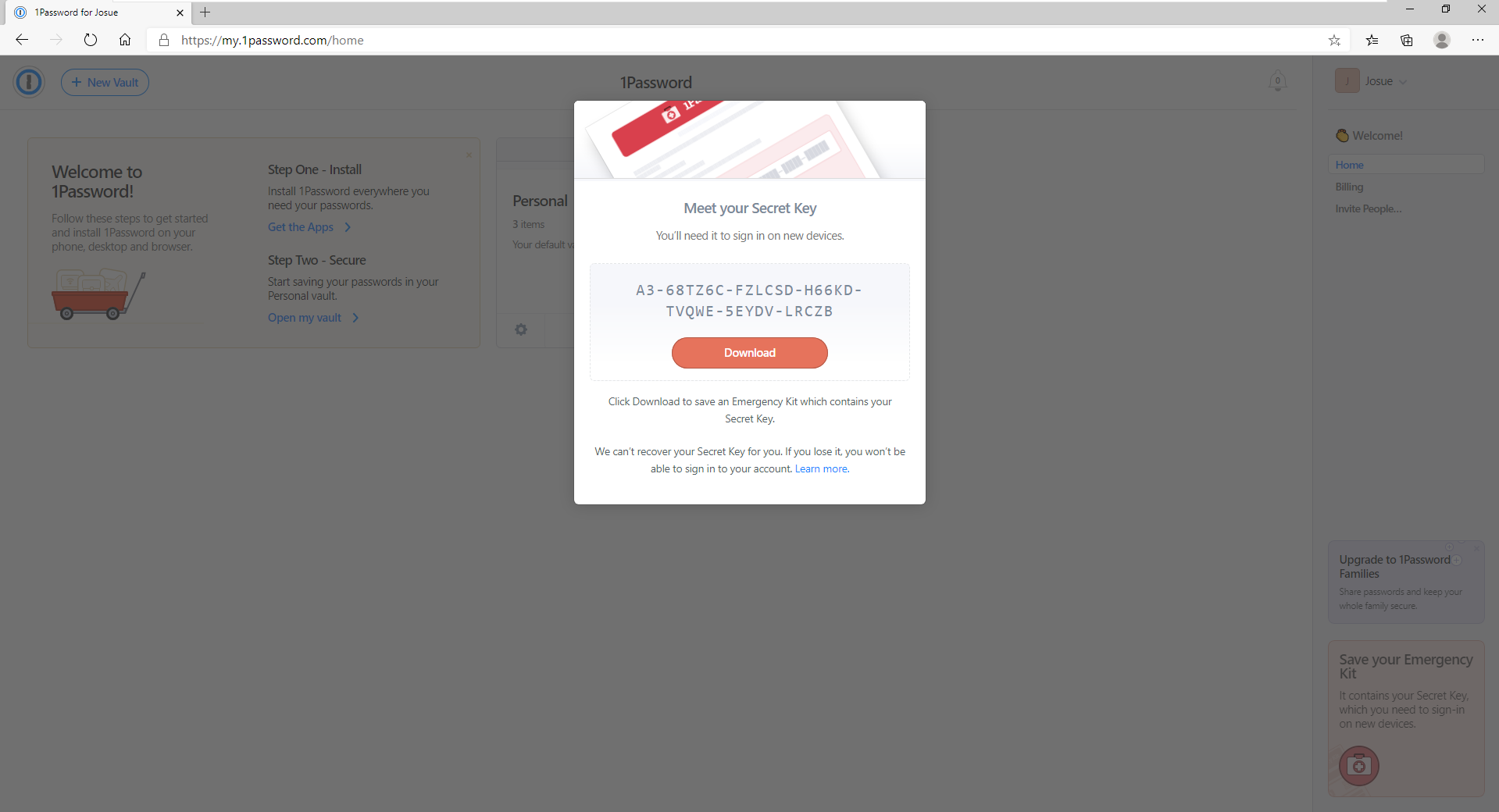
The next step was to obtain the secret key. This is the key used to encrypt data on your 1Password account:
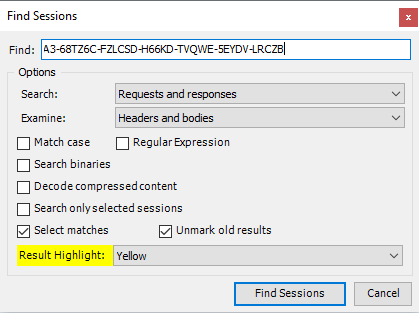
Again using the find feature returns zero results for the secret key:
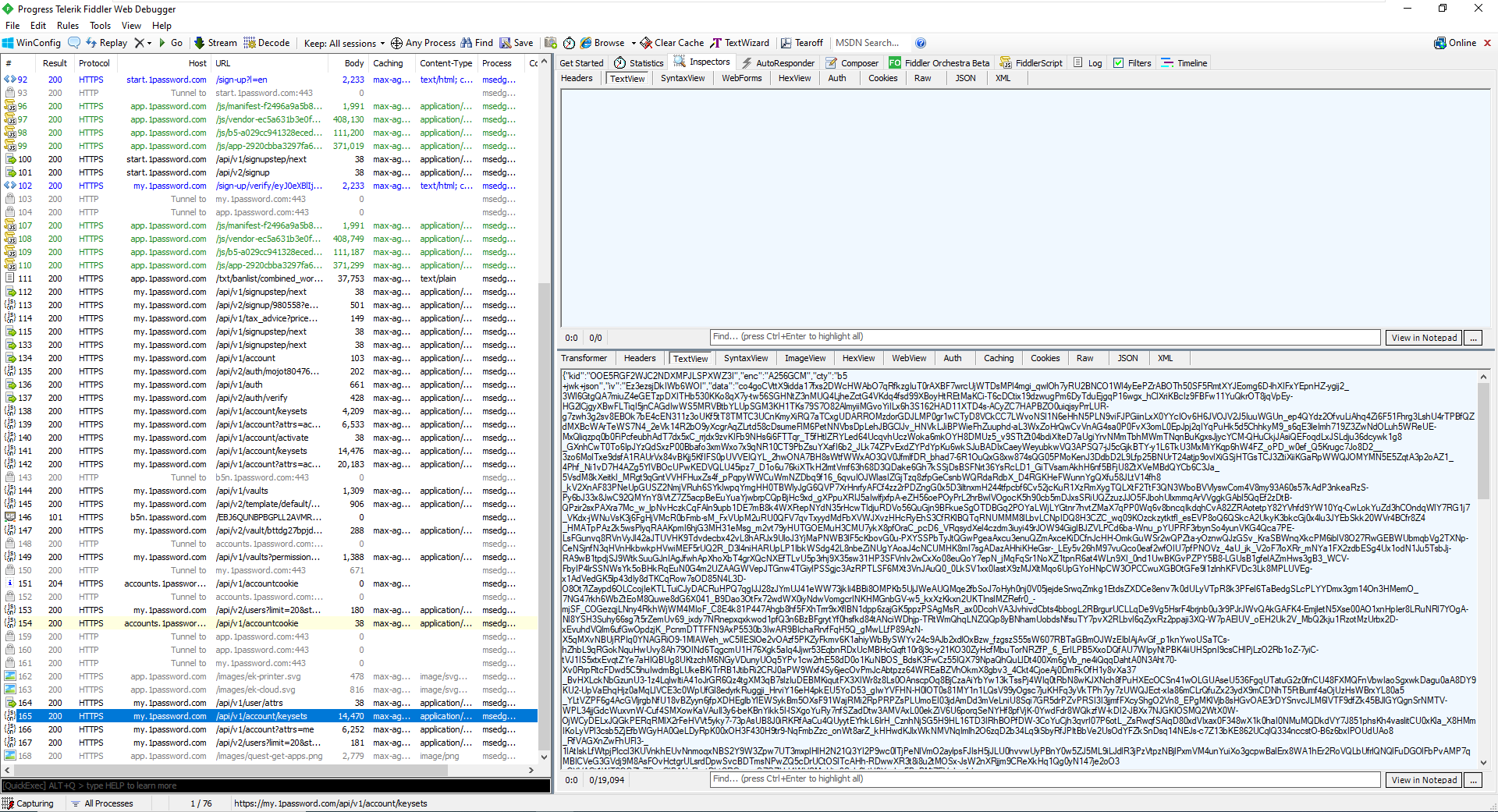
Even downloading the PDF from the initial screen has the data encrypted:
Passwords
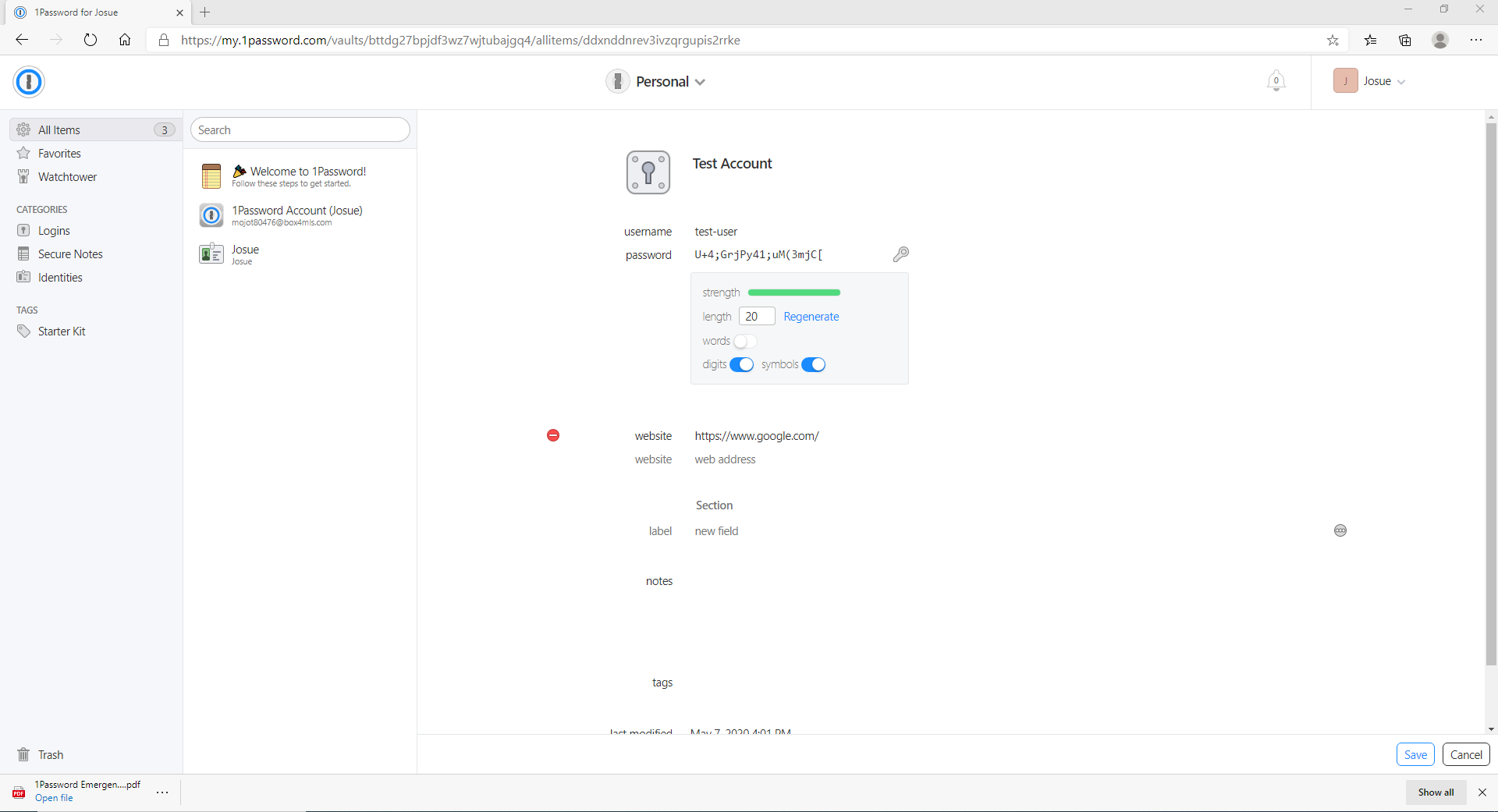
The next step is to see how password for your accounts are handled themselves. For this I created a new Login entry in the Personal vault:
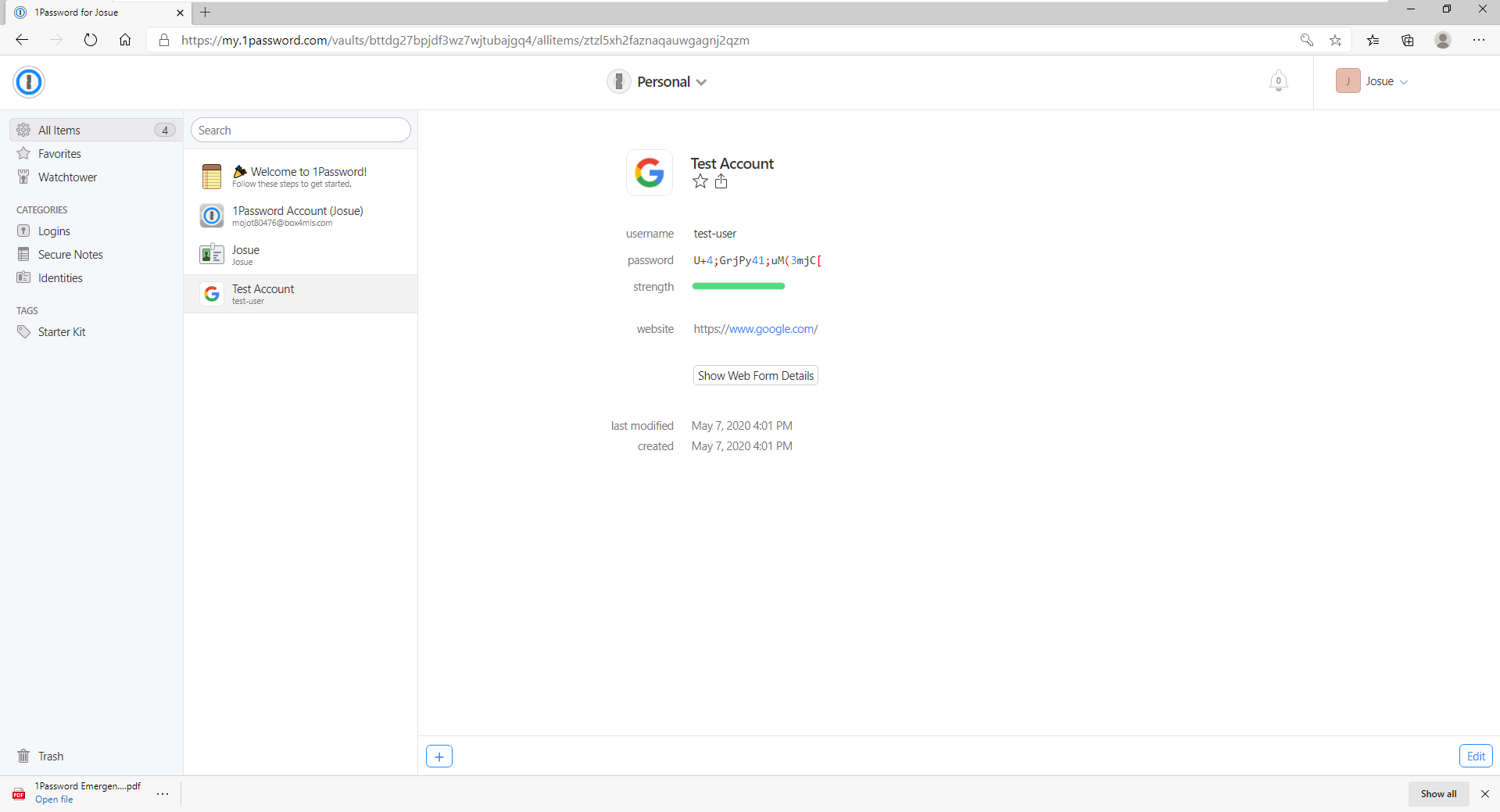
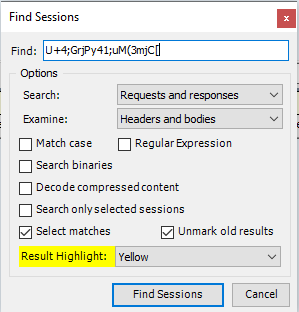
Again using the find feature:
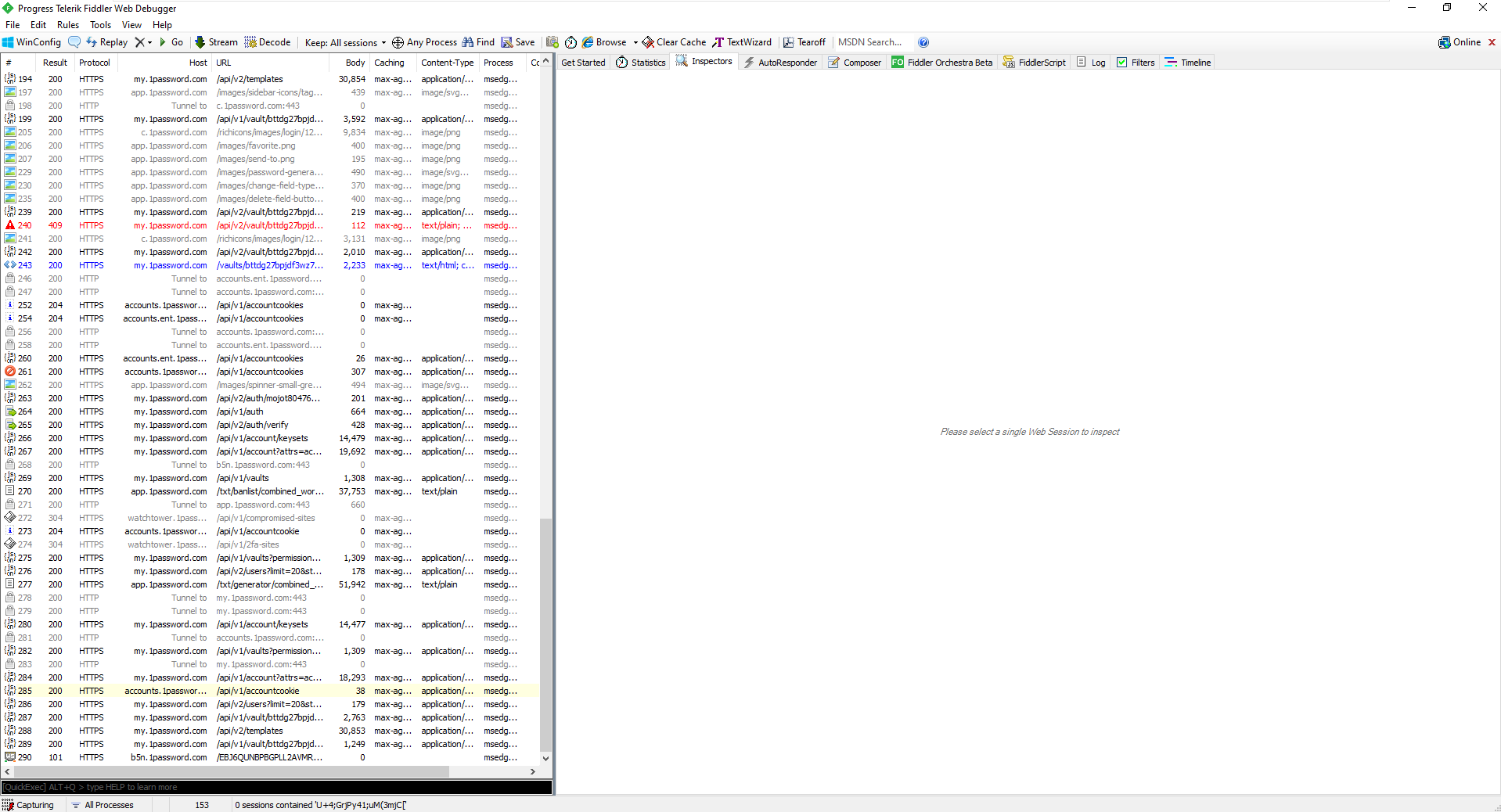
Even searching for "Test Account" (the vault entry name) and "test-user" (the username), returned no results.
This is all because the entries are encrypted client side with your secret key. 1Password does not have access to your data without this key. And as can be seen above, 1Password never handles this key, it is only handled client side. Your secret key itself is never made available in plaintext anywhere on 1Password's systems.
Conclusion
I decided to perform this investigation, since I've seen some have a concern (legitimate) that 1Password has access to all your secret information. They only have access to your encrypted secret information, to which only you have access to the key. Until there is a flaw found in AES-256 (using the GCM mode), there is no feasible way for 1Password (or anyone else for that matter) to be able to gain access to your secret information. And this is the reason why I am comfortable with having my passwords stored in 1Password. It is also worth pointing out that 1Password also have a $100k bounty for anyone who is able to find a flaw in their system. 1Password have also published their whitepaper which goes into great detail of their system and how your secrets are handled. And while I trust what they have documented in their whitepaper and site, I think it is still worth validating it. Which I hopefully have to a large degree.


