I’ve seen recent posts on Twitter calling out security practices such as phishing exercises. While I understand where they are coming from, I feel that they are missing the point of these exercises. In an ideal world, I agree that there shouldn’t be a need for them. We should have the appropriate technology and mechanisms in place to prevent these emails even reaching users in the first place. And have confidence that this will work 100% of the time. But unfortunately in the real-world it doesn’t quite work like this.
The Exercises
So I’m sure that we’ve all been in an organisation where they run a periodic phishing campaign. This involves intentionally sending a phishing email to either the entire organisation or a select few within the organisation. After which some type of report and review is carried out to determine who fell for the email.
Now I totally get the point that this being deceptive with your own employees. As I said in the introduction, in an ideal world it would be great to never have the need for this. But let me ask you this. Would you rather your employees fall for a phishing email that you created (and won’t go any further in terms of the email itself) or an attacker looking to either target individual employees or your organisation?
And here’s the crux, phishing campaigns should be seen as a tool. Not a process or event. They are a tool that helps:
- Ensure existing controls and processes are working as intended
- Identify employees who need further help (additional awareness training and education)
Phishing Campaign as a Tool
And as with most tools, they can be misused. There is a line in terms of targeting your employees. In the past there have been campaigns targeting employees with the promise of bonuses. Now personally I wouldn’t use this approach, but I can see the value in it. Attackers and scammers are not going to care about ethical values. The purpose of the tool is to try mimic the real world, and this is exactly the type of thing that an attacker will play on.
Attackers generally use the following human emotions to get people to fall for their phishing attempts:
- Greed - the promise of additional financial or other reward
- Urgency - the need to complete something immediately
- Authority - scaring the victim if they don’t complete the actions in the email they will have negative consequences to deal with
- Curiosity - having access to something they wouldn’t ordinarily have
One of the strangest campaigns I’ve heard about was a campaign that promised a free turkey (this was run in the US around Thanksgiving). And it worked! Worse yet, employees in the UK found about it and got annoyed that they got left out (of their free turkey, no the campaign).
So as a tool, organisation’s need to be extremely careful about how they run these campaigns. My advice is tailor to your organisation, making sure that it aligns as much as possible to your organisation’s culture and values. If you are unsure, my advice again is to err on the side of caution.
Dealing With the Results
Another extremely important aspect of these campaigns is dealing with the results. These campaigns must not be used as a means to beat employees over. Some things that I recommend:
Do’s
- Be as transparent as possible. Explain why you ran the campaign, and what some of the results where
- When sharing results, make sure that they are anonymised
- Provide support and guidance to those who did fall for the email. This is an opportunity to help those who need it
- Be mindful of how employees could react once they find out about the campaign
- Use overall statistics to identify trends
- Leverage technology as much as possible
Don’ts
- Don’t finger point and call out employees
- Don’t tie results to any performance related measurements, especially promotions, pay increases and bonuses
- Don’t publicly shame employees
- Don’t use this as an excuse to monitor employees
The Other Really Important Benefit
So for me personally this is a big one. While these campaigns are primarily designed to help the organisation itself. However there is an additional benefit to employees. The knowledge and awareness that they gain through these campaigns should carry over to their personal lives. Let me repeat that, but ensuring employees are better equipped to identify phishing emails in the corporate environment, they will likely be able to better spot phishing emails in their personal lives. To me that’s a big win. Why?
Well for a start, personal email accounts are far easier to target. People with personal accounts will likely not have many of the features and technologies in place that organisations have, in terms of combating phishing emails. So if you are attempting to rely solely on technology to solve the problem, employees will be accustomed to “someone else or something else will protect me”. While this may be true when they are in their work environment, this won’t be true at all in their personal lives. They will very likely become a victim as a result unfortunately. And unfortunately the impact for personal victims is likely to be far greater since they don’t have the resources to deal with the repercussions. People’s lives could potentially be destroyed as a result.
I’ve also yet to see any technology do an incredibly successful job when it comes to phishing emails. They do a good job, but there are times when emails get through still. And it only takes that one.
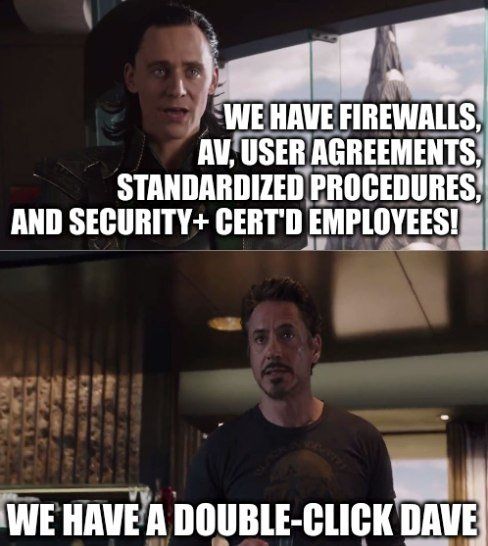
As I mentioned, while technology is important and does help, it doesn’t however stop everything. Like almost everything in cybersecurity, it is both a technology problem, as well as a people problem. And this is why these campaigns are so important. They help you identify your blind-spots and weaknesses in both. And then have the means to address both, especially the people problem. Working with those who need the help and ensure that they are well equipped going forward.
Conclusion
So in conclusion, while I see the arguments against phishing campaigns, I do see the value in them. But only if they are done correctly. I also believe a lot of the arguments against such campaigns are those which haven’t been done well as all, and in some cases one may even question the real motive of them.
In closing I’ll also leave 2 meme’s on the topic that I absolutely love (and remember while technology certainly helps, it won’t stop everything though)!

A bit of a side note, some time back I started a repository on GitHub with the aim of attempting to point out real-world phishing examples, and then document the features of the messages that users should look out for. I haven't added anything for a while unfortunately, but I hope to start adding more in the coming weeks.
You can find it using this link:



